.webp)
- Cybersecurity
- November 3, 2025
Table of Contents
- What is Cybersecurity?
- Basic Cybersecurity Terminologies
- Importance of Cyber Security
- Key Concepts of Cyber Security (The CIA Triad)
- 6 Fundamentals of Cybersecurity
- Cyber Hygiene: Everyday Habits for Safer Online Practices
- Top Cyber Threats to Learn
- Top 7 Cyber Attacks That You Should Know
- Emerging Threats: Quantum Computing and the Future of Cybersecurity
- Building a Safer Digital Future
The internet is playing a significant role in our daily activities and has practically become a necessity for them. We do our jobs on it, we do online shopping, we do online learning, and we also communicate with our family and friends through the internet. However, with the increasing digitization of our lives, there are more risks and dangers that we have to face. Hacking of emails, stealing of money, leaking of personal data, and similar incidents have already been happening quite frequently. This serves as a warning to the entire online user community that there is always a chance to be a victim of cybercrime.
That is why cybersecurity is now a must. In basic terms, cybersecurity means the protection of all your devices, data, and online activities from hackers and scammers. It is not the concern of only large corporations or the government. Ordinary users, students, families, and small business owners are exposed to the same risks.
This article aims to make cybersecurity easy and practical. We will explain the concepts, most common threats, and real-life examples of how the attacks take place. Most importantly, we will give you things you can do to become more secure online.
What is Cybersecurity?
Cybersecurity is defending computers, networks, and digital data from cyberattacks or malicious use. Simply put, a system or set of technologies and processes has been created such that the technology can be trusted and be safe by itself.
In various ways, the system can sometimes stop unauthorized access to an account; at other times, it stops alteration, theft, or destruction of vital records; and lastly, it can keep essential systems such as banking or medical networks and transportation systems operational even if under attack.
You might also hear the term "information security" used. The two are essentially synonymous but not identical.
- Cybersecurity is concentrated on information and systems that are linked to the internet or digital networks.
- Information security is more extensive and covers all types of information, including physical papers retained in offices.
All cybersecurity is information security, but information security is not limited to the digital world.
In today's era, cybersecurity is no longer a choice. It is the foundation that provides us the facility to use technology with ease while signing into email, paying bills online, or setting up entire enterprises in the virtual space.
If one does not have a clear understanding of the terms and concepts used, cybersecurity can be overwhelming. So, before going into depth, let us first clarify some basic terminology that is essential for understanding the concepts.
Basic Cybersecurity Terminologies
Before we go deeper into this guide, it helps to understand some of the most common terms in cybersecurity. Knowing these words will make it easier to follow the concepts and examples that come later.
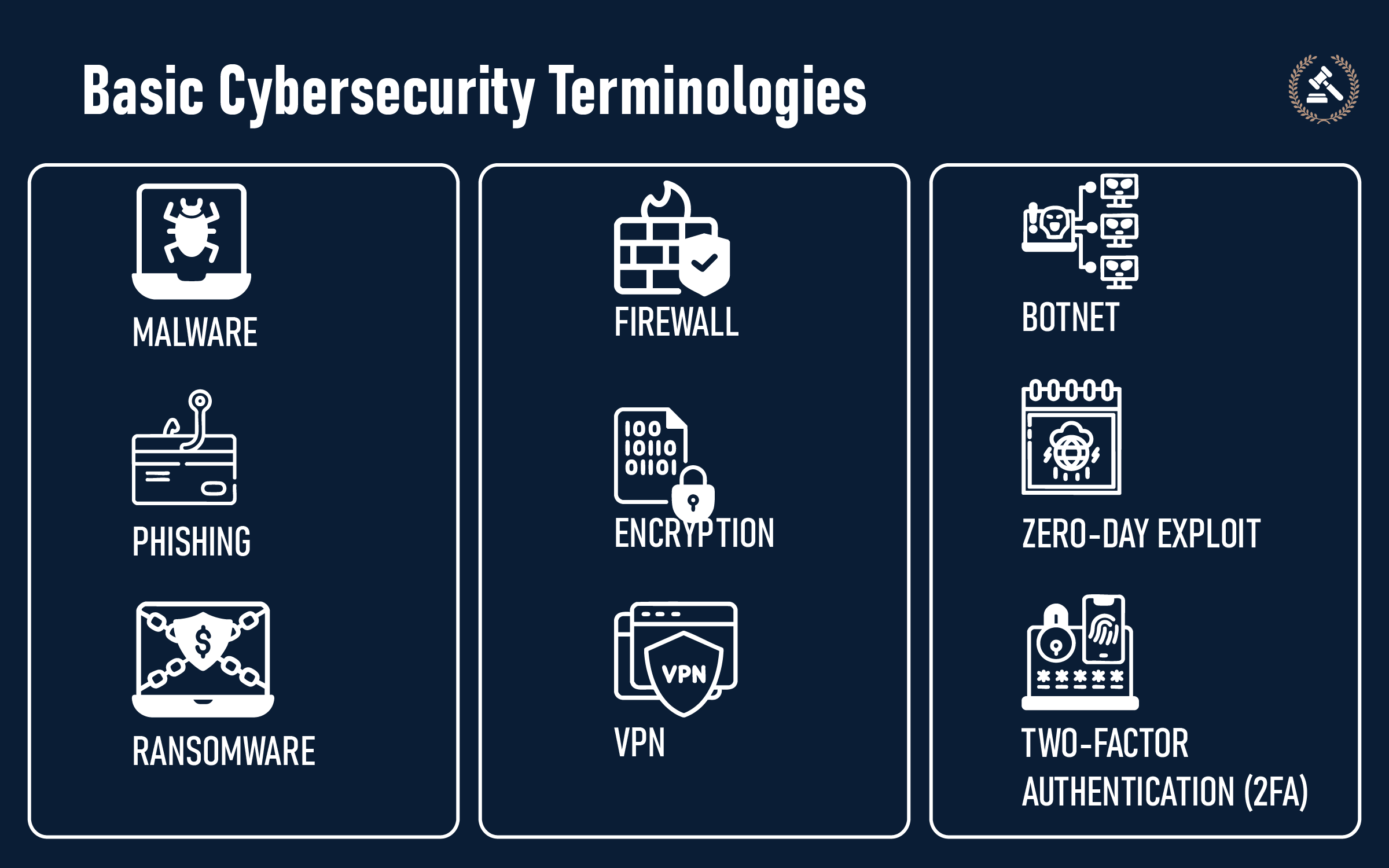
- MalwareMalicious software is what malware stands for in short. Malware covers any harmful program that has the intention to either damage your device, take away your information or monitor your actions.
Example: A deceptive mobile application that, unknown to the user, installs a virus that collects customer information
- Phishing
This is a technique whereby fraudsters dispatch counterfeit emails, texts, or messages impersonating well-known companies to deceive people into revealing sensitive information.
Example: An email appearing to be from a bank requesting you to "confirm" your login credentials. Learn more about phishing scams in this detailed article on online phishing scams.
- Ransomware
Ramsomware is a malware type that encrypts files and asks for a ransom payment to return them.
Example: The documents of a company are encrypted, and hackers demand Bitcoin as a condition for restoring access.
- Firewall
A mechanism that protects a network through supervision and filtering of traffic allowing only authorized users to enter it.
Example: Companies install firewalls to filter out and prevent any suspicious traffic from entering their internal servers.
- Encryption
The alteration of data into a code that is hard to decipher by anyone but the authorized readers.
Example: The apps for messaging take advantage of encryption to keep their chats private and secure.
- VPN (Virtual Private Network)
A service that protects internet activity by creating a secure and private connection.
Example: Employees working remotely use VPNs so attackers cannot track their browsing or steal sensitive company data.
- Botnet
A collection of compromised machines that the attackers can control via remote access. Bots are mainly used to execute big cyberattacks.
Example: an overwhelming amount of traffic from thousands of hacked devices render a business website non-operational by crashing it.
- Zero-Day Exploit
A flaw in a software application that is discovered by hackers before the vendor releases a patch.
Example: a newly found defect in a widely used app that allows unauthorized access till a fix is issued.
- Two-Factor Authentication (2FA)
A two-factor authentication is a verification procedure that has two layers, such as a password and a one-time code. This added security ensures that it is even harder for attackers to access the accounts. Find out more about it in our Complete Guide to Two-Factor Authentication (2FA).
Example: Accessing an email account using a password and a code that has been sent to a phone.
Learn more about different Must-know Cyber Terms here.
When these terms are understood, it becomes quite obvious that cybersecurity is not merely technical jargon but rather a real-world necessity for both individuals and organizations.
Importance of Cyber Security
Cybersecurity is of prime importance as it safeguards the digital data and computers that we use every day. Without strong security, personal data, business dealings, and national security remain under continuous threat. Its importance is viewed on three levels: individual, organization, and government.
For Individuals
Cybersecurity protects personal data such as passwords, financial information, medical information, and classified messages. If wrongly taken or abused, the consequences can range from identity theft to financial losses to long-term privacy issues. A lapse by a user going wrong about any single action-touching on a weak password or clicking on a bad link-can have very dire consequences.
For Businesses
Cybersecurity is very important to a company’s continuity and trust. A security breach could result in the exposure of sensitive customer data, which could lead to severe financial penalties, and the company’s hard-earned brand reputation might be affected negatively. Moreover, data protection is still part of the regulations for most companies, and the failure of compliance would result in legal consequences prescribed by the law. In addition, a company with a good cybersecurity posture will prevent downtime and thus, always be available for business.
For Governments and Nations
On a national scale, cybersecurity entails interconnectedness with critical infrastructures like hospitals, transport, energy, and defense systems. An attack on any of these will have an impact on millions of individuals at the same time and will result in total disruption of the provision of crucial services. To safeguard important information about its citizens the government, uses cybersecurity means, as the trust of its citizens is its credibility in trust establishment, and furthermore they need protection from some areas of cyber warfare or espionage.
Understanding its importance brings us to the three core principles that guide all cybersecurity measures: confidentiality, integrity, and availability, often referred to as the CIA triad
Key Concepts of Cyber Security (The CIA Triad)
At the center of cybersecurity is a framework known as the CIA Triad. This has nothing to do with intelligence agencies. Instead, it stands for three key principles: confidentiality, integrity, and availability. Together, these principles form the foundation for protecting digital systems and information.
-
Confidentiality
Confidentiality is related to keeping information private and also that the information is accessible only to the correct people. Once information is given to unauthorized persons, it can no longer be considered protected.
Example: Online banking protects confidentiality by using passwords and encryption, so only the account holder can access bank balances and send money.
-
Integrity
Integrity is the requirement that data be reliable and unchanged. If data is changed without permission, it is unreliable.
Example: In health care, patient records must be reliable. If a hacker changes a patient's medical history, a physician may make an unwise medical decision based on incorrect data.
-
Availability
Availability is the assurance that systems and information are available when needed. Lengthy access to the system is meaningless even though the data is highly secure and correct.
Example: Denial-of-service (DoS) attacks that are used to compromise the IT systems of a hospital disallow availability, requiring lengthy access to vital patient information.
These principles shape the practical steps and systems that make up the fundamentals of cybersecurity in everyday use
6 Fundamentals of Cybersecurity
Cybersecurity is based on a collection of fundamental practices that form its foundation. These practices lower risks, safeguard information, and ensure systems operate as anticipated. Familiarity with these basics is essential for individuals and organizations.
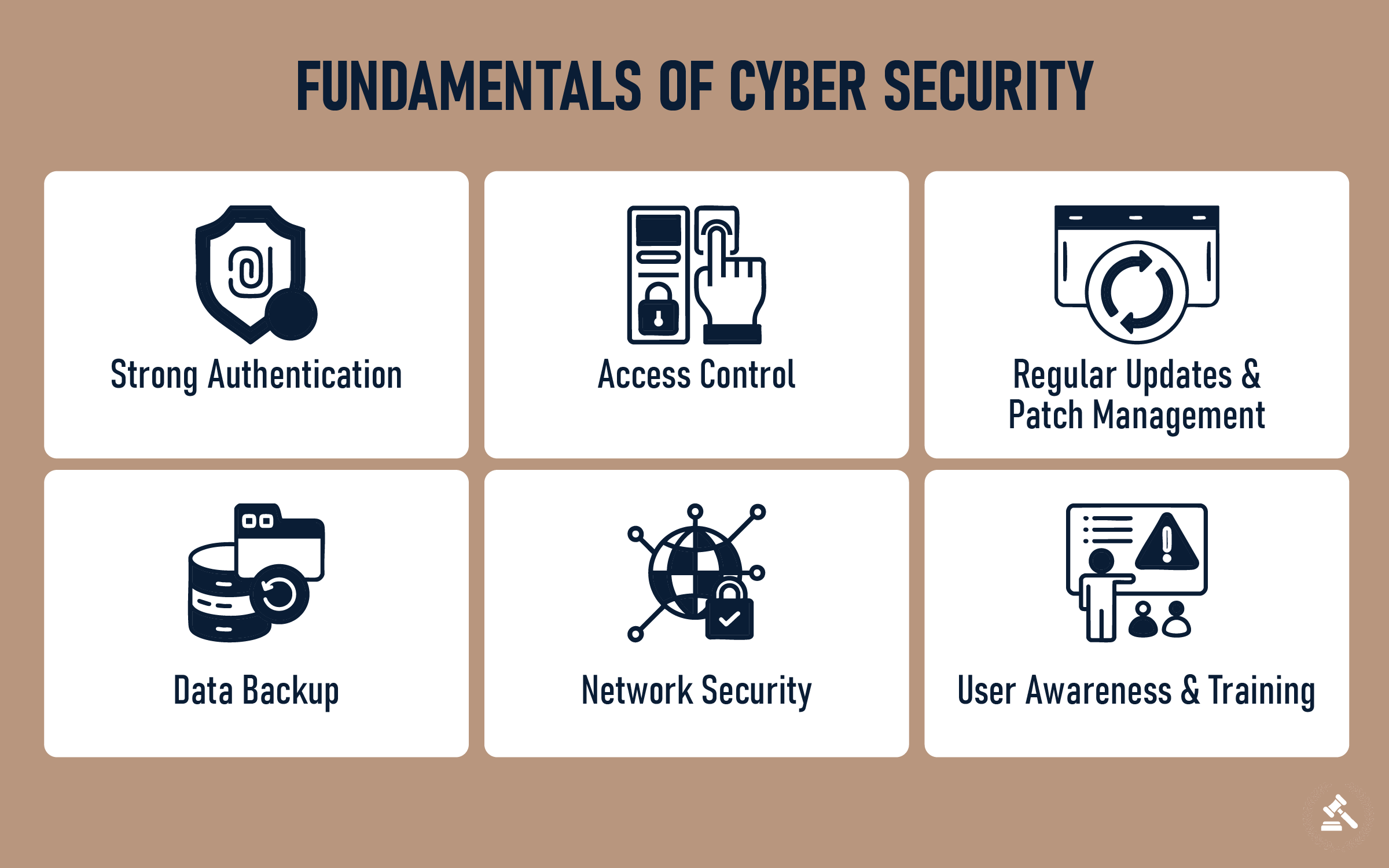
-
Strong Authentication
Authentication is regarded as the procedure of confirming the identity of a person thus allowing user access. It is a pretty normal thing to ask a user for a password, assuming it to be secure, only to get hacked. A guessing technique can also be applied to use the user's credentials for the hacker's benefit. A second step is establishing a code from a text to make it even harder for others to access.
-
Access Control
In order to secure the limitations of the opportunities to data and systems, it is not required that everyone has access to these data or systems. The practice of limiting access to others not only diminishes the chance of misuse but also accidental harm.
Example: An accountant in a company needs to locate and review the financial records, and the medical staff needs to locate and review patient records.
-
Regular Updates and Patch Management
Applications and software usually have exploits that hackers can take advantage of upon successful access. Management of updates and patches can make it harder for hackers to find those weaknesses and exploit them.
Example: The update to a phone may close a bug that a hacker could exploit in order to steal data.
-
Data Backup
A backup is a duplicate of important data stored in a different location from the original system. It helps you ensure that data can be recovered when it is lost, damaged, or held hostage as a result of an attack.
Example: A business can keep functioning by recovering its data from a backup even if ransomware is encrypting its documents.
-
Network Security
Networks must be secured so unauthorized control cannot be maintained or gained. Firewalls, secured wireless, and monitoring software help manage the flow of traffic and can help eliminate some of the malicious behaviors.
Example: A firewall can stop potentially malicious connections from reaching a company's systems.
-
User Awareness and Training
There is only so much technology can do to protect individuals and organizations. It is up to the individuals to notice when they should pay attention to signs like unusual emails and webpages that look like authentic sources and understand the requirement to take action.
Example: An employee notices and deletes a phishing email before their organization is compromised.
While fundamentals provide the framework, staying safe online also depends on simple daily habits. This is where cyber hygiene comes into play.”
Cyber Hygiene: Everyday Habits for Safer Online Practices
Cybersecurity basics have always been the foundation but we should not forget that the actual protection is based on the small, everyday actions we take on the internet. Here is where the concept of cyber hygiene becomes important. Just as it is necessary to maintain and/or secure your physical place, whether it is home or office, the daily practices to be implemented are really important for the safety of your personal information, money, and even the reputation of your business.
Examples include: complex and unique passwords, two-step-factor authentication, keeping devices up to date, and only clicking on links or email attachments from verified persons or sources. These may sound basic, but often make the biggest difference in avoiding breaches and attacks.
Cyber hygiene is in many ways, our first line of defense. It helps individuals and organizations protect themselves and remain resilient before advanced tools and technologies step in. If you want to learn more about cyber hygiene, we’ve created a complete guide on cyber hygiene, with practical tips and a checklist to follow
Even with strong habits in place, the digital world is full of evolving dangers. To understand the risks we face, let’s look at the most common cyber threats.
Top Cyber Threats to Learn
Cyber threats are threats that can damage computers, cell phones, and data on the internet. They can be from hackers, malware, or even inadvertently from individuals who use a system. Learning about these threats is the first step towards keeping them out.

-
Malware:
Malware is short for malicious software. These applications are designed to harm devices, steal data, or secretly monitor activity.
Example: A computer virus that propagates via email and hinders business systems or deletes critical files.
-
Phishing:
Phishing is where perpetrators send spoofed emails, messages, or texts to trick individuals into divulging financial or personal information.
Example: A bank-like message that requests an employee to click a link and type in log-on information.
-
Ransomware:
Ransomware is malware that encrypts files and requires payment to decrypt them.
Example: A corporation's financial information is encrypted, and hackers request cryptocurrency before they will decrypt it.
-
Insider Threats:
Often, threats come from inside the organization. Sometimes employees or contractors take advantage of their access, either on purpose or by accident.
Example: An employee downloads client details unauthorized
-
Denial-of-Service (DoS) Attacks:
Hackers bombard a site or system with artificial traffic in a DoS attack, rendering it inaccessible to legitimate users.
Example: An online store is bombarded with requests and goes offline during business hours.
-
Social Engineering:
Social engineering attacks people rather than systems. Attackers exploit human trust to steal information.
Example: A scammer phones an office masquerading as IT support and convinces staff to disclose passwords.
-
Advanced Persistent Threats (APTs):
In an APT situation there are prolonged, directed attacks where hackers silently gain access to networks, and steal data, one piece at a time, over several months. APT situations are usually targeted at large companies or government departments.
Example: Hackers routinely accessed a corporation's research database for months to steal trade secrets.
Learn in more detail about cyber threats in this detailed article.
Threats are potential dangers, but attacks are when those dangers turn into action. Here’s how cyberattacks unfold and why they can be so damaging.
Top 7 Cyber Attacks That You Should Know
Cyber attacks are deliberate actions taken by criminals to break into systems, steal data, or cause damage. While cyber threats describe potential risks, cyber attacks are the actual attempts to exploit those risks. Below are some of the most common types of businesses and individuals face:
1. Password Attacks
Hackers try to steal or guess passwords to gain access to accounts and systems.
Example: Attackers use automated tools that test thousands of password combinations until the correct one is found.
2. Man-in-the-Middle (MITM) Attacks
A criminal secretly intercepts communication between two people or systems to steal information in this kind of attack.
Example: Hackers have access to a public Wi-Fi connection to get banking login details in the middle of the transmission.
3. SQL Injection
Attackers gain access to the database of a website by injecting destructive code through input fields, such as login forms, etc.
Example: A hacker submits a malicious script in the username box to infiltrate a company database and retrieve customer data.
4. Cross-Site Scripting (XSS)
Malefactors insert malicious codes into web pages that get executed whenever a user accesses the page.
Illustration: Entering into an online community where an invisible script is working to confiscate the cookies and login credentials of all users.
5. Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS)
Perpetrators bombard a system with fake traffic to cause it to crash or become unresponsive.
An example would be the shutting down of an online retailer’s site during a big sale event because of flooding the site with millions of phony requests from attackers.
6. Supply Chain Attacks
Hackers do not directly attack a company but go after the suppliers or organizations that supply services to get inside. Example: A hacker infects an application update, and that update is sent to all the businesses that install it, thus deploying malware to all those businesses.
7. Zero-Day Attacks
Hackers take advantage of a security flaw before the developer can provide a fix. Example: A new application has a bug that nobody knows about, and an attacker exploits it on the same day it’s discovered.
Cyber attacks continue to expand in scale and complexity. It does not take much for businesses to find themselves exposed to serious financial loss and reputational harm; even one weak link could allow a hacker to turn nothing into something irreversible, such as a compromised password or unpatched system.
Learn in more detail about cyber attacks in this detailed article.
Emerging Threats: Quantum Computing and the Future of Cybersecurity
- Quantum Power vs Encryption: Quantum computers have the potential to crack the encryption technologies that are widely being practiced, like RSA and ECC, thus revealing secret information.
- Data Privacy Threats: It is very likely that the hackers will henceforth keep their data encrypted for a longer period and will decrypt it later when the computing power of quantum is sufficient: "Collect now, decrypt later."
- Industry Readiness: Organizations are starting to investigate post-quantum cryptography (PQC) and quantum-safe encryption standards
- AI for Quantum Cybersecurity: Artificial intelligence is being used to develop quantum-resistant algorithms and identify vulnerabilities before attacks can take place.
For a full guide on quantum computing and its implications for cybersecurity, see our dedicated Quantum Computing and Cybersecurity blog.
Building a Safer Digital Future
Cybersecurity is no longer optional; it is a requirement for all. It acts as the shield with which we protect data concerning individuals, businesses, and even national systems so that we can operate safely in an interconnected world.
Being protected would mean more than just using the right tools; it demands constant awareness, discipline in good security protocols, and a willingness to accept the study of new threats. By adhering to such principles, neither business nor individuals will only withstand today's threats but also face tomorrow's challenges.
Cybersecurity is not just about technology; it is about trust, safety, and resilience in the digital age. The more we understand it, the stronger we become against those who seek to exploit weaknesses.
FAQs (Frequently Asked Questions)
The best first step is to enable Two-Factor Authentication (2FA) on all your critical accounts, especially your primary email. Your email is often the key to resetting all your other passwords, so protecting it is crucial. 2FA provides a powerful second layer of defense that stops hackers even if they manage to steal your password.
For everyday browsing at home on your secure Wi-Fi, a VPN isn't strictly necessary. However, it becomes very important when you use public Wi-Fi (like at a coffee shop, airport, or hotel). On these open networks, a VPN encrypts your connection, acting like a private tunnel that prevents snoops and hackers on the same network from seeing your activity.
It's impossible to remember dozens of unique, complex passwords. The solution is a password manager. These are secure apps that create, store, and auto-fill strong passwords for you. You only need to remember one strong master password to unlock the manager. It's one of the most effective tools for boosting your online security.
Antivirus software is an essential tool that helps detect and remove known malware, but it's not a complete solution. It can't protect you from phishing attacks where you are tricked into giving away your password, nor can it stop every brand-new "zero-day" threat. Think of it as one important layer of security, but you still need to practice safe browsing habits.