
- Cybersecurity
- September 30, 2025
Table of Contents
Social media has evolved into an inseparable part of our personal and professional lives. The whole process during which we communicate, share our achievements, or get updated, the same data can silently disclose much more than what we actually project as our online persona. Our digital activities, such as sharing photos and updates, constantly add to the online identity we manage. Places we live, work, or celebrate might not be very revealing, but the whole lot together forms a data path that hackers find very advantageous.
Hackers are on the rise, using social media to covertly gain access to other people's identities, and by linking together small pieces of publicly available information that are seemingly innocent, they can impersonate a person, alter password accounts, or gain entry to critical systems. Even information that is made public on professional networks can be used by attackers to design targeted phishing or business email compromise attacks. The most unfortunate thing about the situation is that people are not aware of the risk posed by their day-to-day posts.
In the next section, we'll examine how hackers study social media behavior, what methods they employ to acquire sensitive information, and what you can practically do to safeguard your identity before it is stolen.
What Are Hackers Really Looking For on Your Social Media?
Most individuals believe hackers just want passwords. However, in fact, they search for little bits of personal data that, when combined, tell them a lot about you. Every update, image, or comment assists them in piecing together an entire portrait of your life. Once they possess that, it is easy for them to steal identities or conduct frauds. The following are the important types of data they seek and how they use it.

1. Personal information
Your birthdate, hometown, previous addresses, or pet's name might be considered as minor facts but they are still regularly used as security question answers. By knowing this much about you, hackers can reset your passwords, make fake accounts, or impersonate you through verification tests.
2. Daily routines and lifestyle
The things you do every day, where you go on holidays, your job or new purchases tell more than you realize. Your holiday plans give away your absence at home. Posting your job title or company works for them to compose convincing spear-phishing emails. Little pieces of information are used to create scams that look very real and personalized.
3. Photos and videos
Pictures can reveal a lot. They might show private items like bills, license plates, or the inside of your home. Even the background can give away your location or income level. Hackers study these details to learn more about your life and your assets.
4. Social connections
Your friends and followers are a circle of trust. When hackers know who you communicate with, they can masquerade as you or one of your contacts to propagate scams. This is because their messages appear authentic, causing others to share more information or funds.
In the next part, we’ll explore how attackers turn these details into real damage and how you can protect yourself before it happens.
How Do Hackers Exploit Social Media Information?
When hackers compile your information, they have a variety of methods to steal your identity. Most of these methods are based on you unknowingly assisting them. Below are the most frequently used tactics by hackers:
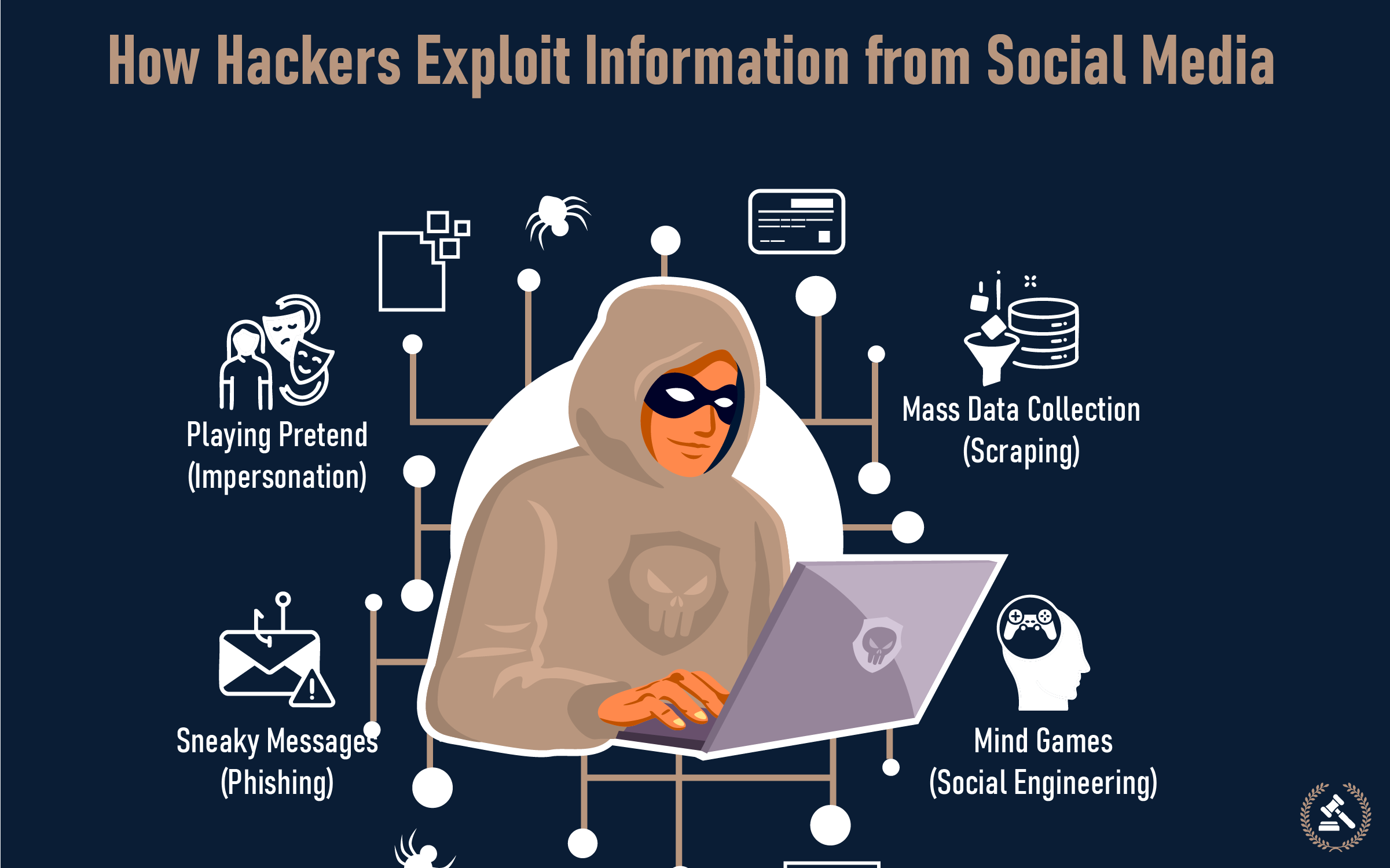
1. Sneaky Messages (Phishing)
This refers to the sending of what appear to be genuine messages (like DMs, emails, or messages) but in reality, are not. They could be pretending to be a friend whose account was hacked, or customer service for a brand, or even a notification about the issue with your account. Their purpose is to get you to click on a harmful link or to give them your login details or personal information. Sometimes, they even take information from your social media (like where you work or when you traveled) and then use that to make these messages sound credible; this attack is called spear phishing..
2. Playing Pretend (Impersonation)
Identity theft criminals often create false accounts using your pictures and personal details to pretend to be you or a person close to you. Then, they might trick your friends and even further use your data to get the phone company to transfer your number (SIM swapping) and consequently access your other profiles.
3. Mass Data Collection (Scraping)
Think of this as digital vacuuming. Hackers use special tools (or just a lot of patience) to quickly gather all the public information from your social media profiles. Their goal is to build a detailed profile of your life, which they can then use for future targeted scams, credit fraud, or even sell to other criminals.
4. Mind Games (Social Engineering)
Social engineering is all about brain manipulation and deceiving you into assisting with a little technical skill and effort. You may get an invitation to participate in those amusing quizzes that require you to answer your security questions (like naming your first pet or telling the name of the street you lived in as a child), or you could even be tricked into sharing your sensitive data by creating an imaginary emergency.
When Impersonation Becomes Identity Theft: A Real-Life Case
To really grasp how social media is being abused, let's consider a current, real-life scenario that took place in June 2025 in the USA. It is the story of George Tsaftarides (84) and Charles Ray (85), two older men who just lived out their lives on TikTok. Unfortunately, scammers hijacked their videos and photos to set up imitation social media accounts pretending to be them. These scammers added fake, sad stories, like needing money for a struggling animal sanctuary, and employed these stories to sell affordable goods like slippers and blankets.
This was not hacking but social engineering in which scammers exploit trust to deceive people. Although we can't quantify how much money was lost, the real George and Charles suffered greatly from this scam and significant damage to their good reputation, as their videos were exploited to defraud others. Having TikTok and other sites delete these fake accounts was enormously challenging. This tale points to a grave and rapidly developing problem. Cases of people using false identities online have risen by 148% in just one year. The growth of AI tools has made it easier for fraudsters to create fake profiles and convincing content. It shows why being alert and cautious online is now more important than ever.
How to Protect Yourself from Social Media Identity Theft?
Real-life cases like the one mentioned above can be worrying, but you’re not powerless. You have more control over your online safety than you might think. By following a few simple habits, you can greatly reduce the risk of becoming a target for identity theft. Strengthening your digital protection takes less effort than most people expect.
Here are some practical steps you can start with
1. Strengthen Your Digital Defenses
Treat your online accounts like sensitive business data, review privacy settings regularly, and limit who can see your posts or tag you.
- Lock Down Your Privacy Settings: Frequent checks on the privacy settings of your profiles in the social media realm (Facebook, Instagram, TikTok, LinkedIn, and so forth) are advised. If a privacy setting made your life private last year, it might not do so today, for these platforms tend to undergo regular engendering. Always select the "Friends Only" or "Connections Only" setting for the creation of personal posts and for photos so that one can very much limit people from prying into your life. Additionally, never forget to approve any tags to be authorized in case they would tag you in any photograph or post.
- Fortify Passwords & Enable 2FA: Your password is your first line of defense. Create long, unique passwords (12-16 characters or more) mixing letters, numbers, and symbols for every account. Never reuse passwords if one gets hacked; they all could. This is why it is recommended to use password managers for better safety. Even better, enable Two-Factor Authentication (2FA) on every single account that offers it (social media, email, banking). This means even if a hacker has your password, they can't get in without a second code, usually sent to your phone. It's like needing two keys for one lock!
2. Common Sharing Mistakes Scammers Count On
Every post you make contributes to your "digital footprint." Being aware can prevent a lot of heartache.
- Think Before You Post: Every post has its own signature, so it is good if you share with consideration. Avoid disclosing your full birthdate, address, or phone number in public posts. Do not participate in “fun” online quizzes that require personal information, as they usually reflect typical security questions. It is also safer not to reveal your exact whereabouts at the moment or to divulge your travel itinerary.
- Identify Red Flags: The hackers depend on your ignorance of red flags. Take care not to respond to messages from "friends" that are strange, poorly written, or that ask for money or confidential information, claiming their account has been hacked. If you receive unsolicited password reset notifications, do not click on any links; go directly to the service website. Always distrust suspicious links or attachments, even if they look like they are from someone you know.
- Be Careful with Connections: It’s best to keep your social network limited to people you know and trust. Before accepting a friend request, check the profile carefully; if it seems new or unusual, confirm directly with the person. Maintaining a smaller, trusted network helps reduce the risk of impersonation or fake accounts.
3. Monitor Your Digital Presence
Even with precautions, it's best to keep an eye on things.
- Monitor Financial Statements Periodically: Review your bank and credit card statements regularly for any unusual charges or activities.
- Check Credit Reports: Obtain your free annual credit report and review for any new accounts that have been opened in your name without your authorization.
By embracing these habits, you can safely enjoy the advantages of social media without practically negating them through your exposure to identity theft and by establishing a robust foundation of online safety.
What to Do If Your Identity Is Compromised?
Even under the most ideal situations, a scammer might still get a way through. In case you have an identity theft or misuse suspicion, do not be afraid. The most crucial thing is that you take quick action and adhere to these unambiguous steps:

- Act Fast to Limit the Damage:
- Alter passwords at once: Change passwords of all impacted accounts (social media, email, banking, etc.) to new, strong, unique ones immediately. As a precaution, consider using password managers.
- Activate 2FA on all accounts: If you have not done it yet, enable Two-Factor Authentication (2FA) for all your important online accounts.
- Analyze devices: Perform a thorough check for any disguised dangers on your computer and mobile by running antivirus/anti-malware software..
- Alert Key Organizations:
- Notify Banks & Credit Cards: Call the fraud department of any bank or credit card company where you see suspicious activity.
- Report to Social Media Platforms: Inform the specific platform about the fake profile or compromised account.
- Contact Law Enforcement: If significant financial theft occurred, or you're facing serious harassment, file a police report.
- Keep Detailed Records:
- Log Everything: Write down dates, times, who you spoke to, and any reference numbers for all communications.
- Save Evidence: Take screenshots of suspicious messages, fake profiles, or any fraudulent transactions.
- Don't do It Alone: Get Expert Help:
- Navigating identity theft can be overwhelming, involving banks, credit bureaus, and potentially legal steps. You don't have to tackle it by yourself.
- Connect with LegitAssure: If you're unsure how to proceed, or need expert guidance to recover your identity, LegitAssure is here to help. We connect you with trusted digital forensics experts, legal advisors, or specialized recovery teams tailored to your situation, simplifying the process of finding reliable assistance when you need it most.
Smart Practices for Lasting Online Security
Social media offers incredible ways to connect, learn, and share, but as we've seen, it also presents a fertile ground for identity theft. From individual subtle signs to high-level impersonation scams like the one that George and Charles faced, the threats exist and are constantly changing. However, smartness is your greatest security. Creating a strong barrier around your online identity is through taking proactive measures such as reducing your privacy settings, employing strong passwords and 2FA, and being careful about what you share. And in case the worst happens, remember that quick and sensible action is your fastest way back to normalcy.
For a deeper look at how to strengthen your defenses across all areas of digital life, explore our comprehensive guide on cybersecurity. It covers practical steps beyond social media that can help safeguard your personal and financial information in today’s connected world.
FAQs (Frequently Asked Questions)
Identity thieves are often looking for puzzle pieces like your full name, birth date, hometown, pet names, old addresses, or details about family members. They use these public tidbits to guess security answers, build fake profiles, or try to access your accounts. They know what data hackers steal from social media can be incredibly valuable.
Absolutely, yes! Posting vacation photos can alert criminals that your home is empty. As for those "fun" quizzes asking about your first car or favorite teacher, they're often designed to gather common security question answers. This is how seemingly harmless social media activity can open doors for identity theft.
The single most impactful step is to enable Two-Factor Authentication (2FA) on every account that offers it (social media, email, banking). This adds a crucial second layer of security, meaning even if someone gets your password, they can't log in without a unique code sent to your phone. It's the best way to secure social media accounts.
If you suspect your identity was compromised via social media, act fast! Change all affected passwords right away and turn on 2FA. Next, contact your bank and credit card companies to report suspicious activity. Also, report the issue to the social media platform itself. These are essential steps after social media identity theft.
Look for red flags like profiles with very few posts, no mutual friends, or duplicates of people you already know. Be highly suspicious of messages that sound urgent, have odd grammar, or ask you to click strange links or send money. Knowing how to spot fake social media profiles and phishing messages is crucial for your safety.