
- Cybersecurity
- November 26, 2025
Cybersecurity has evolved from an IT concern to the very foundation of a secure and reliably operating enterprise. No matter the industry, be it finance, healthcare, retail, or consulting, having a basic knowledge of the subject will help you in early risk identification, costly mistake prevention, and safeguarding the organization’s reputation.
And to achieve this, technical expertise is not mandatory. What you need is an understanding of the key concepts, elaborated with the help of simple terms.
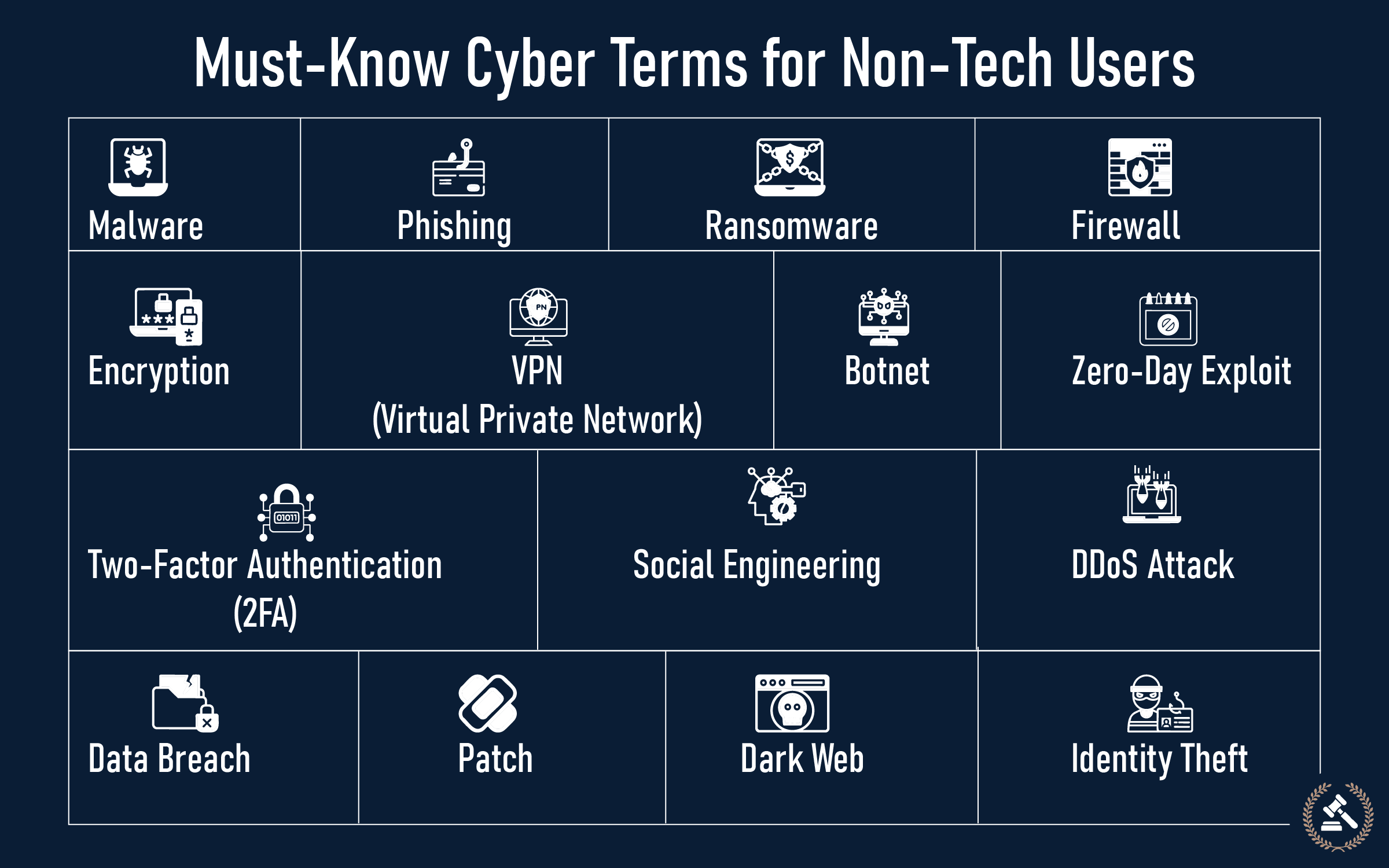
Basic Cybersecurity Terminologies
We have discussed 15 essential cyber terms below with proper explanation and business examples from real-time scenarios, so that even a non-techie can shift confidently to the digital realm
1. Malware
Bad computer programs that mess up your computer on purpose. They sneak onto computers and cause trouble. You might get them from email attachments or sketchy websites. They work quietly in the background.
Example: A big store had workers download something they shouldn't have. Bad guys got into their payment system. The store got in trouble, and customers stopped trusting them.
2. Phishing
Trick emails that look real but aren't. Scammers impersonate famous companies and try to steal your passwords or money info. These fake emails look super real now.
Example: A money manager received an email that appeared to come from his boss. The email asked him to send money fast. He did it, but it was fake. The company lost millions of dollars.
3. Ransomware
Computer viruses that lock up all your files. The bad guys want money to unlock them. Even if you pay, you might not get your stuff back. Plus, they'll probably try again later.
Example: A hospital couldn't access patient files because of ransomware. Doctors couldn't do their jobs properly. The hackers wanted lots of money to fix it.
4. Firewall
Like a security guard for your computer network. It watches what comes in and goes out. Good stuff gets through, bad stuff gets blocked. Every business needs one.
Example: A bank set up good firewalls around its customer website. When hackers tried to break in, the firewall stopped them before they could cause damage.
5. Encryption
Encryption is a method of concealing the information in such a way that only specific individuals are able to understand it. It's done by using a secret language. Even a thief, if he manages to take it, won't be able to make sense of it without the decryption key.
Example: A medical clinic had all patient records encrypted. When criminals accessed their system and took files, they were unable to decipher the content, as it was all in code.
6. VPN (Virtual Private Network)
Creates a secret tunnel for your internet connection. Nobody can spy on what you're doing online. Really important when using public WiFi at coffee shops or airports.
Business Example: Business travelers used VPNs when working from hotels. This kept hackers from stealing company secrets when they used hotel internet.
7. Botnet
Thousands of hacked computers that work together like robots. The bad guys control them all at once to attack websites or send spam. Your computer might be part of one without you knowing.
Example: An online store got flooded with fake visitors during a big sale. Real customers couldn't buy anything. The store lost money and made customers mad.
8. Zero-Day Exploit
A secret weakness in computer programs that nobody knows about yet. Hackers find these holes before the good guys can fix them. It's like having a broken lock that you don't know is broken.
Example: A shipping company used old computer programs with secret holes in them. Hackers used these holes to mess up deliveries and make customers angry.
9. Two-Factor Authentication (2FA)
Two-factor authentication adds a second step to your login process. Along with your password, you confirm your identity using a code sent to your phone or a quick fingerprint scan. This extra layer makes it much tougher for anyone to access your accounts without permission.
Example: An investment company made all clients use two passwords. When hackers stole regular passwords, they still couldn't get in because they needed the second code too.
10. Social Engineering
Social engineering targets people rather than systems. Attackers often pose as trusted contacts and try to convince you to share passwords or sensitive details. They rely on pressure, urgency, and familiarity, making it easier to slip past traditional security measures if you’re not alert.
Business Example: A fake caller pretended to be a boss who forgot his password. He was so convincing that the help desk worker reset it for him. The hacker got into the important company's stuff.
11. DDoS Attack
Like having too many people try to get into a store at once. Hackers flood websites with fake visitors so real people can't use them. The website crashes from too much traffic.
Example: An airline's booking website got flooded with fake traffic during busy travel time. Real customers couldn't buy tickets. The company lost tons of money.
12. Data Breach
When someone breaks into a company's computer and steals private information. It could be customer names, credit cards, or business secrets. Companies get in big trouble when this happens.
Example: Hackers broke into a big store's payment system and stole millions of credit card numbers. The store got sued and had to pay huge fines. Customers stopped shopping there.
13. Patch
Like a band-aid for computer programs. When companies find problems with their software, they make patches to fix them. If you don't put the patch on, hackers can use the broken part to get in.
Example: A bank didn't want to update its computers because it would take time. Hackers used the unfixed problems to steal money from customer accounts.
14. Identity Theft
When someone steals your personal information and pretends to be you. They might use your name to buy things, open bank accounts, or sign contracts. Really hard to fix once it happens.
Example: Bad guys stole a company boss's identity and used it to sign fake contracts. The company lost partnerships and lots of money.
15. Dark Web
The secret, hidden part of the internet where criminals hang out. You can't get there with regular browsers like Chrome. Hackers sell stolen passwords and credit cards there. It's like the bad neighborhood of the internet.
Example: After hackers broke into a bank, they found thousands of customer passwords being sold on the dark web. The bank had to tell everyone and spend tons of money fixing the problem.
Cyber Awareness is Business Awareness
Gone are the days when cybersecurity was just a footnote in the tech manual; it has now become one of the main things in business resilience and trust. It is essential for every employee, irrespective of their technical expertise, to know these 15 terms at least to identify risks and make better decisions. Every organization should include this education in its security awareness program. When employees know the language of cyber threats, they can alert themselves to the danger, keep away from the usual pitfalls, and help the IT departments in maintaining the security of the organizations.
In the end, cyber awareness is equivalent to business awareness. A better-informed workforce means a stronger company defense against the ever-changing digital threats. To get more insights, delve deeper into our Complete Cybersecurity Guide and be prepared to deal with risks in advance.
FAQs (Frequently Asked Questions)
The non-technical user must be aware of words like phishing, malware, ransomware, firewall, VPN, two-factor authentication (2FA), encryption, data breach, etc. These terms help you identify common threats and understand how to protect personal or workplace data.
When employees are aware of terms such as phishing, spoofing, and social engineering, they are capable of identifying suspicious emails, unsafe links, and unusual login attempts, thus reducing the likelihood of accidental data leaks and strengthening the overall organisational security.
Encryption renders your data unreadable to hackers, and 2FA means the addition of a second step, like an OTP, to prevent unauthorized logins. All these simple security steps together work well to reduce account hacking risk considerably.
Start with terms related to everyday risks: phishing, strong passwords, malware, and 2FA. These give immediate protection and help build confidence before learning more advanced concepts like network security or encryption protocols.