
- Cybersecurity
- November 24, 2025
Table of Contents
Today's digital environment presents more cyber threats than ever before. The adoption of work-from-anywhere policies, cloud services, mobile devices, and third-party services has blurred the lines of the traditional network perimeter, making the exploitation of weaknesses much easier to conduct for attackers. Most organizations still use legacy security models based on the assumption that anyone who has access inside the network is trustworthy; that assumption is no longer valid.
Consequences are severe: data breaches, ransomware attacks, insider threats, and compliance violations disrupt operations, damage reputations, and result in massive financial losses.
This is where Zero Trust comes in. Using a "never trust, always verify" philosophy, Zero Trust authenticates and authorizes every user, device, and application on a continuous basis, before every critical resource. Implementing Zero Trust minimizes attack surfaces, prevents lateral movements of threats within the network, and enhances overall cybersecurity resilience. This, in turn, fosters confidence to operate securely in an ever-increasingly complex digital environment.
What is Zero Trust?
Zero Trust is a modern security model that stipulates that no one should be trusted by default, neither inside nor outside the network. It differs from traditional security methods that rely on protecting the perimeter: the Zero Trust model grants access to resources only after the continuous verification of the user's identity, assessment of device posture, and evaluation of contextual factors. This principle enforces least-privilege access to ensure that users can access only what they need, while micro-segmentation limits the attacker's access through division into smaller, controlled zones of the network.
Continuous monitoring and real-time analysis of behavioral signals identify potential malicious or abnormal activity. By applying the Zero Trust model, an organization can drastically reduce risks, ensure sensitive data protection, maintain regulatory compliance, and provide safe access for users working from everywhere.
Key Principles of Zero Trust
The Zero Trust model works on a few principles that make it suitable to secure modern workspace networks. These are mentioned as follows:
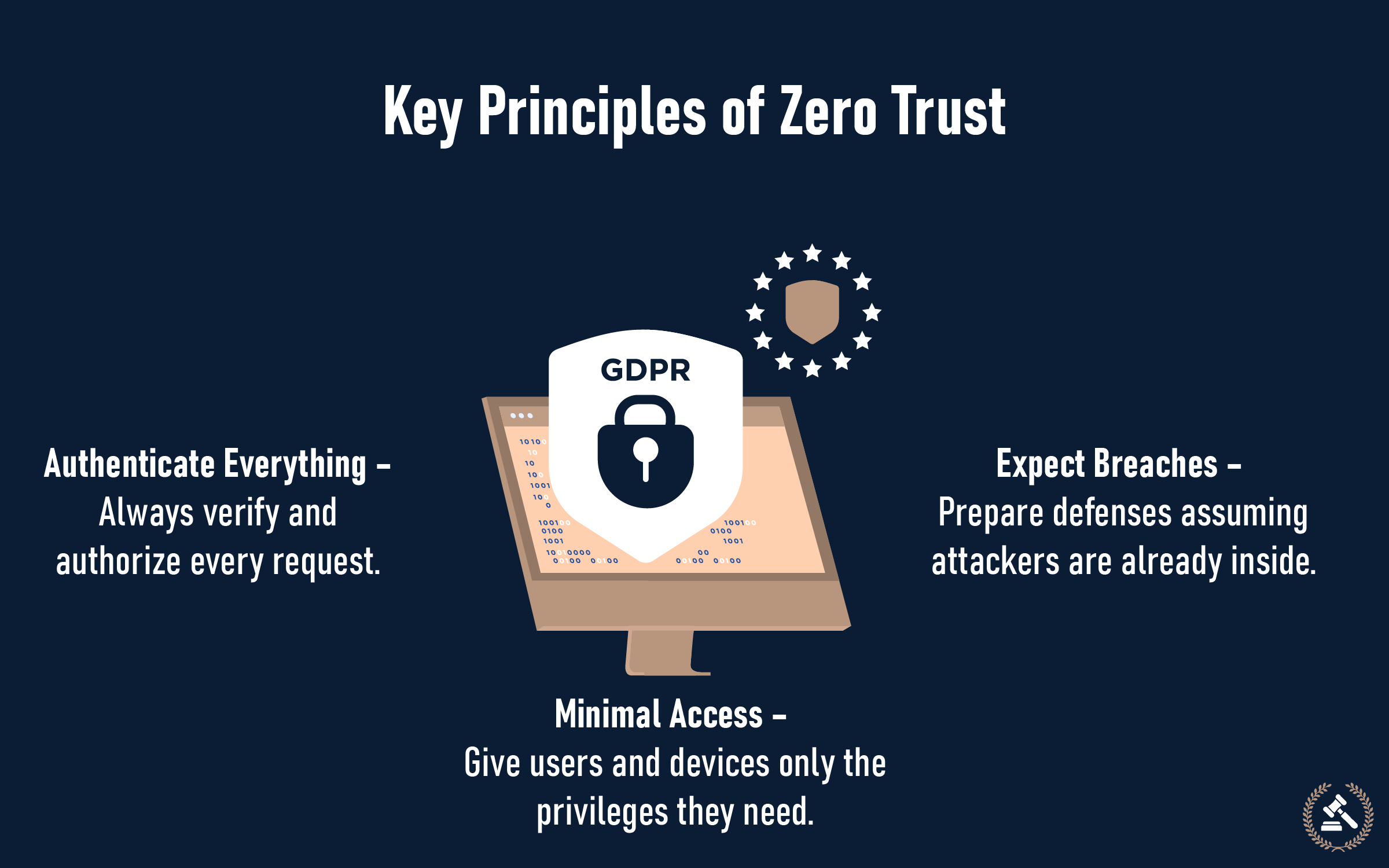
Authenticate Everything – Always verify and authorize every request.
All access requests will be required to be authenticated and authorized via methods such as multi-factor authentication, device health check, and ongoing risk assessment, such that no device or user will be inherently trusted.
Minimal Access – Give users and devices only the privileges they need.
Applications, users, and devices need only minimal permission in order to perform duties given to them, primarily enforced through role-based control and permissions on a just-in-time level, restricting harm inflicted due to compromised accounts.
Expect Breaches – Prepare defenses assuming attackers are already inside.
Treating every system as though attackers may already be inside, which drives organizations to monitor continuously, segment networks, and detect anomalies quickly to contain threats before they escalate.
After knowing these principles, a question arises: why do enterprises need a zero security trust model, and how does it help them to stay safe? Continue reading even if you are not an enterprise, because Zero Trust is more useful than you think.
Why Enterprises Need Zero Trust
Zero Trust is an approach that enhances overall security inside out. Here are a few reasons why each enterprise should adopt this concept.
1. Rising Cyber Threats
Traditional perimeter-based security models are no longer enough as attackers use sophisticated methods like phishing, ransomware, and insider threats to gain access. These attacks often bypass firewalls and other perimeter defenses by exploiting human error, compromised credentials, or vulnerabilities in third-party applications. As threats evolve, enterprises need adaptive security that monitors and validates every request in real time.
2. Remote Workforce
Today, employees are working from multiple devices and diverse locations; the traditional concept of ‘office network’ is now distributed everywhere. A Zero Trust model ensures secure access by verifying both user identity and device health, no matter where the employee is located.
3. Cloud Adoption
Unlike traditional data centers, the cloud doesn’t operate within a single secure perimeter. Sensitive information is spread across multiple providers and systems, creating new access controls, encryption, auditing, and breach notification. Zero Trust frameworks directly support compliance by enforcing least privilege access, tracking user activity, and strengthening overall data security.
Zero Trust security is useful, but one should get to know the exact makeup of the model.
Core Components of Zero Trust Architecture
An abstract concept of Zero Trust is often difficult to understand. Hence, here is the simplified explanation of the core components of Zero Trust.
-
Identity and Access Management (IAM)
Strong identity verification is at the core of Zero Trust. Technologies like multi-factor authentication (MFA), single sign-on (SSO), and adaptive authentication only grant access to authenticated users. Access policies use context like user role, device type, and location and decrease the likelihood of illegal access.
-
Device Security
All such devices that aim to connect, manage, or personalize must be brought up to security parity before granting access. It involves validation against endpoint protection, operating system enforcements, and security configurations. By validating device health, organizations make sure vulnerable or non-compliant devices aren't an attack pathway.
-
Network Segmentation
Zero Trust assumes that breaches will and can happen. Micro-segmentation ensures that if attackers somehow infiltrate the network, they remain isolated in a small area. High-value targets are segmented, and access is tightly locked down, restricting lateral movement, and the overall attack surface area is known as network segmentation.
-
Data Protection
Data is the end goal of cyberattacks. Zero Trust requires encryption of sensitive data at rest and during transit, such that even data that has been intercepted can't be viewed. Data accesses have rigorous policies such that the use and sharing of data are audited and tracked.
-
Continuous Monitoring
Security is not a periodic check; it's a process. With AI, machine learning, and advanced analytics, Zero Trust continually monitors user activity, network traffic, and system activity. If anything unusual or suspicious happens, Zero Trust triggers alerts or automated response actions to help organizations detect and contain threats in real time.
With the advancements, there are pros and cons to every single thing. Along with the benefits, Zero Trust also has challenges.
Benefits and Challenges of Zero Trust for Enterprises
The table represents the benefits and challenges of the Zero Trust security model.
| Sr. | Benefits | Challenges |
|---|---|---|
| 1. | Stronger defense against modern cyber threats. | Legacy systems that are hard to integrate. |
| 2. | Reduced attack surface through granular access control. | Initial cost and complexity of deployment. |
| 3. | Improved compliance and audit readiness. | Change in management, like educating staff and updating processes. |
| 4. | Better visibility into user and device activity. | Scalability concerns across large or distributed environments. |
| 5. | Enhanced security posture for hybrid and cloud environments. | Performance impact due to continuous authentication requirements. |
As the table itself says, there are more benefits than challenges. The challenges are quite adoptable. Hence, it is viable to adopt a Zero Trust security policy.
Best Practices for Adopting Zero Trust
So, in case you decide to adopt the Zero Trust model, here are a few best practices that will make the process easier.

1. Focus on Identity First
Zero Trust begins with good identity and access management (IAM). Organizations need to enforce multi-factor authentication (MFA), demand stringent password policy enforcement, and use single sign-on (SSO) across the board. By securing user identities, firms reduce the opportunity for credential-based assaults, the most common point that cyber attackers use to get into a network.
2. Identify Key Assets
Before deploying Zero Trust controls, firms must be aware of what's most in need of protection. That way, firms can ensure high-value assets receive maximum protection while creating a plan of action to achieve broader security coverage.
3. Divide and Protect Networks
Rather than depending on a perimeter alone, Zero Trust implements micro-segmentation to keep critical workloads and systems isolated. By breaking down the network into smaller sections with customized rules regarding access, even if a hacker penetrates a section, they can't travel effortlessly throughout the environment. That containment approach greatly reduces possible damage.
4. Monitor and Evolve Continuously
Zero Trust is not a “set it and forget it.” Organizations must continuously scrutinize user activity, device health, and network traffic to detect anomalous activity. With the help of AI-driven analytics, policies can be continuously revised to address new threats to keep the security architecture improving against those emergent perils.
5. Adopt Zero Trust Step-by-Step
Applying Zero Trust to a whole enterprise can be intimidating. What companies should do instead is apply it on a phase-by-phase basis, beginning with high-risk sections and increasing step by step. That way, teams can become experts, achieve quick wins early on, cause minimal disruption, and eventually create a safer security transformation.
Avoid the Regret
Zero Trust is no longer optional for enterprises; it's becoming a strategic necessity. By enforcing strict access controls, continuous monitoring, and assuming that breaches are inevitable, Zero Trust empowers organizations to secure their data, systems, and users in today’s dynamic digital environment. In the upcoming growing times, network traffic is also increasing. No one knows which network belongs to legitimate holders and which one belongs to scammers. In this case, the Zero Trust model is a saviour to all upcoming security-related issues.
FAQs (Frequently Asked Questions)
It protects against modern cyber threats, insider risks, and breaches. With remote work, cloud adoption, and increasing regulations, Zero Trust ensures stronger control over data, applications, and user access.
Traditional security relies on perimeter-based defenses (trusting everything inside). Zero Trust, however, removes implicit trust and continuously verifies identity, device health, and user activity regardless of location.
When implemented correctly, Zero Trust balances security with user convenience. Adaptive authentication, single sign-on (SSO), and automated policies help ensure a smooth experience without compromising protection.
No. While enterprises benefit greatly, small and mid-sized businesses can also adopt Zero Trust principles to secure remote work, cloud services, and sensitive data.
Zero Trust enforces strong identity verification, access control, and monitoring, which align with compliance frameworks like GDPR, HIPAA, and PCI-DSS.